How do you make sure your Azure Edge devices are secure and cannot be tampered with?
This is the job of the Azure IoT Edge Security Manager.
More information can be found here: https://docs.microsoft.com/en-us/azure/iot-edge/iot-edge-security-manager?view=iotedge-2018-06
The key principals of the Security Manager is that it protects all of the Edge components and devices by abstracting the secure silicon hardware.
OEM can also utilise this abstraction to provide integration with Hardware security modules (HSM) or Trusted platform chips (TPM)

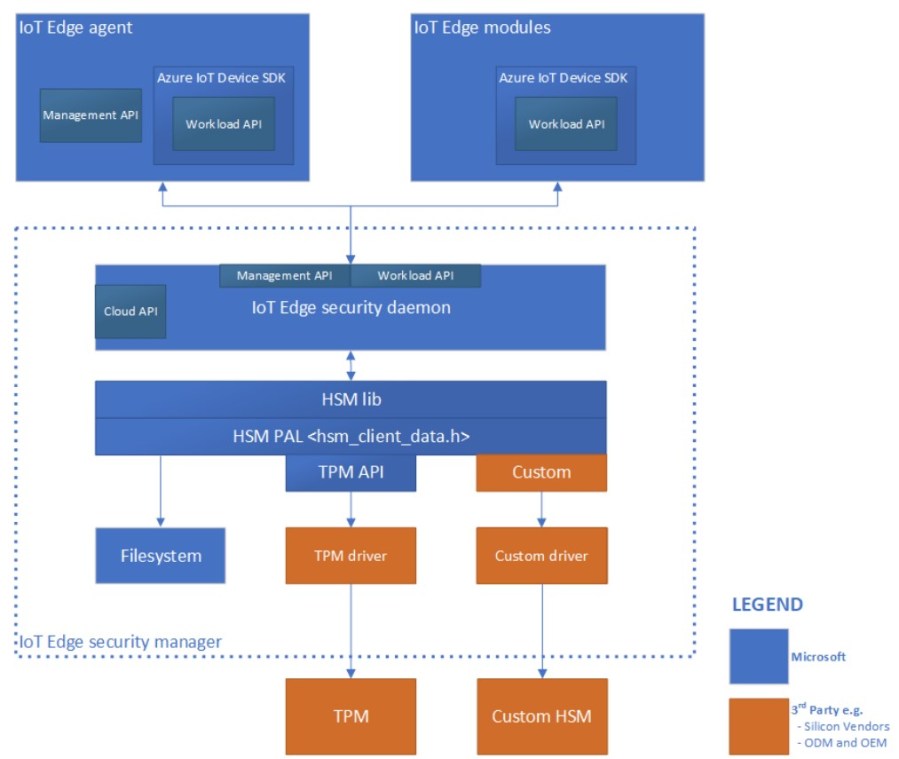
The IoT Edge security manager is comprised of three components:
- IoT Edge security daemon.
- Hardware security module platform abstraction Layer (HSM PAL).
- Optional but highly recommended hardware silicon root of trust or HSM.
Architecture of IoT Edge security daemon
Integration and Maintenance
Microsoft manages and maintains the codebase for the IoT Edge security daemon on GitHub here: https://github.com/Azure/iotedge/tree/master/edgelet
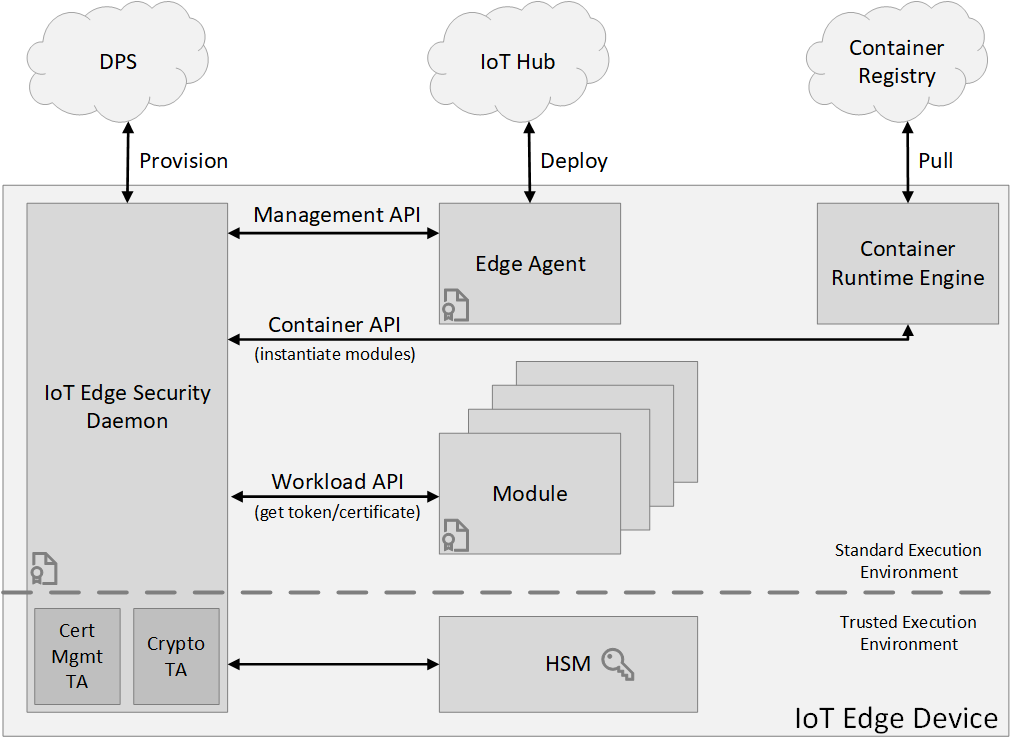
All provisioning and services are deployed and managed via the IoT Edge Security Daemon which is accessed via the Edge Agent container image (module) that is deployed to each edge device as part of the Deployment process.
IoT Edge Certificates link
Generally speaking there are two common scenarios for configuration of IoT Edge Certificates.
Either, the end user of a device will purchase their own certificate, or the device manufacturer may have preconfigured a device for use with certificates and the end user will need to utilise these in order to configure an appropriate attestation method:

Dev/Test implications
To ease development and test scenarios, Microsoft provides a set of convenience scripts for generating non-production certificates suitable for IoT Edge in the transparent gateway scenario. For examples of how the scripts work, see Create demo certificates to test IoT Edge device features.
Confidential Computing Applications on IoT Edge
This type of application is encrypted in transit and at rest, meaning that the decryption can only take place inside a trusted execution environment. These types of applications can be deployed as Edge modules.